An End-to-End email encryption program - Protects email at rest and in motion
Try for free now
The free trial period is 60 days after which no sending or receiving is possible unless a license is obtained. The stored emails can be viewed also after the trial period.
Superior protection for the real world
EndCryptor protects old encrypted emails - that were copied by an adversary when they traversed the internet - also then when the adversary gets current encryption keys by hacking into user's computer. The software automatically recovers from the attack when users exchange emails. The adversary will lose the ability to decrypt new emails.
Easy to use
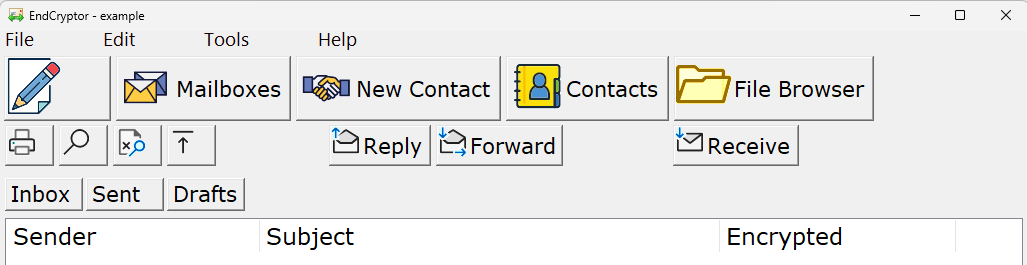
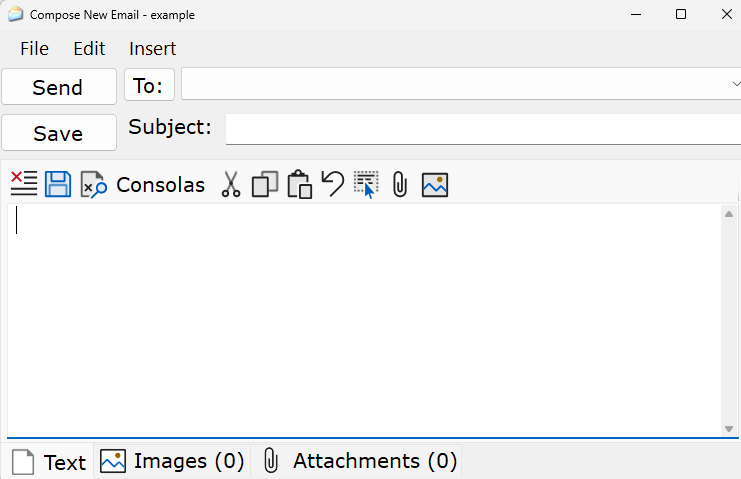
No knowledge of cryptography is required. The user interface is similar to a typical email client. User's current email account is used to deliver the encrypted emails.
End-to-End Encryption
The email is encrypted at sender's computer and it can be decrypted only at true receiver's computer.
Quantum attack resistant
It may be possible that before the year 2030 there will be computers that can break current classical public keys. EndCryptor uses classical public keys and new quantum attack resistant public keys. Note that otherwise current encrypted traffic can be copied and decrypted by quantum computers when they become reality. USA's ‘NIST Internal Report NIST IR 8547 ipd’ states: 'organizations must begin the migration to post quantum cryptography today to avoid having their encrypted data exposed once quantum computers become operational in the future. This threat, often referred to as “harvest now, decrypt later,” underscores the necessity of acting immediately...'
State of the art cipher and public keys
Public key technology: classical: Curve25519, quantum attack resistant: Kyber-1024 (ML-KEM-1024), FrodoKEM-1344 and mceliece6688128f (round 4). Kyber is an official standard of USA, the variants of Frodokem and Mceliece are recommended by Germany's Federal Office for Information Security, see BSI TR-02102-1. The public keys are used in a hybrid setup - this means that an adversary must be able to break all of them. Hybrid setup is used because quantum attack resistant technology is relatively new. The hybrid key setup is done according to the 'Concatenate hybrid key agreement scheme' of ETSI report TS 103 744 V1.1.1 (ETSI is a European Standards Organization (ESO). .. the recognized regional standards body dealing with telecommunications, broadcasting and other electronic communications networks and services.)
Features:
- Both the sender and the receiver must have EndCryptor installed. An email account on email server is needed - same account (i.e. user's current email account) can be used for unencrypted emails and encrypted emails. Encrypted emails are typed using EndCryptor and they are sent and received using EndCryptor. An encrypted email is a file that is an attachment in an ordinary email. The sending and receiving is enabled by defining user's email account's settings into EndCryptor.
- The size of all attachments together in an email must not exceed 2 TB (terabytes). If the encrypted email’s size exceeds a user defined limit a window is shown from which a big encrypted email file can be dragged or copied to a cloud service.
- The sent and received messages are stored in encrypted form on a user’s computer – the user can view their decrypted contents when correct entry password to EndCryptor has been given. The stored messages can be searched, moved between different user creatable mailboxes.
- Messages can be exported in eml format. They can be imported into email archiving solutions. They can also be viewed by many email client programs or dragged and dropped into an existing local email folder. The export feature allows the user to have a complete cleartext archive of the communication.
- The stored messages can be backed up by copying and the backups can be decrypted using a personal or a company-wide (optional) export key. EndCryptor can take a backup of the security database and restore it. That backup can be encrypted. The stored emails can also be backed up by EndCryptor immediately after they have been written to disk.
- Compression of plaintext. Required amount of random bytes are added to hide the length of this compressed plaintext - encrypted messages have different sizes even if their decrypted content is the same.
- A message may have more than one receiver. Contacts can be grouped.
- If an Internet connection is considered to be too risky then EndCryptor can be run entirely disconnected from the network. When a message is encrypted a list of its receivers can be stored in a text format, the message and the list of its recipients can be stored in user given folder. The encrypted message and this list are moved to the actual sending machine using removable media. When decryption is needed the encrypted message is delivered to the receiving EndCryptor again using removable media.
- EndCryptor can be set to monitor some user given folder for new encrypted messages.
- The security database and the stored sent and received messages can be moved to removable media and accessed from it. Thus it is possible to use EndCryptor both from office and laptop computers. The size of an empty security database is about 1 MB.